And yet… we treat them like an afterthought. Or worse, like a seasonal craft project. Time to bust a couple of myths!
Myth #1: If it’s complicated, It’s Secure:
You’ve seen this one before: P@ssw0rd!2025#
Looks great. Has all the things you typically think of as a strong password. So secure. So compliant. So predictable.
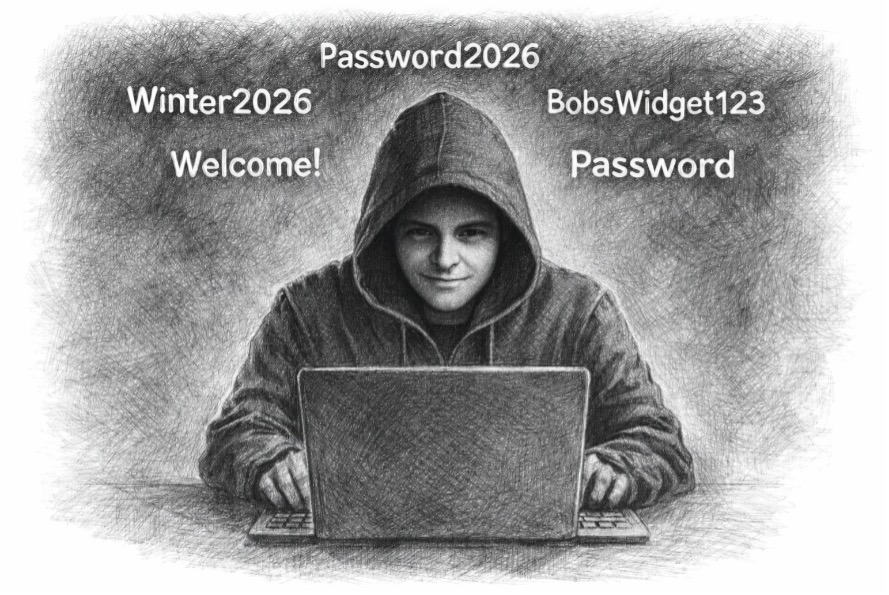
Here’s the problem: Attackers don’t sit there guessing one letter at a time. They use automated tools that try common patterns. And guess what tops the pattern list?
- Password + year
- Season + year
- CompanyName + 123
- Welcome + !
- Password [Password is the most commonly compromised password for decades]
Complexity rules without randomness are just fancy-looking weak passwords.
Myth #2: I’ll Just Use the Same Password Everywhere:
Here’s how this strategy ends:
- Random retail site gets hacked and you get that random notification in the mail and do nothing.
- Your email + password show up in a data dump.
- Attackers test that combo against your company: Email, Network / VPN, Payroll, and Cloud apps.
Password reuse turns someone else’s breach into your breach.
What Actually Works:
- Use a Password Manager: This is not an excel spreadsheet called passwords, paper notes with your password but an actual tool. Password Managers generate long, random passwords, store them securely, and eliminate password reuse. You only remember one strong master password to get into the tool.
- Don’t Want to Use a Tool – Fine: Use long Passphrases such as MyCat$IsAwesome! [just an example and don’t try this at home kids].
- Turn on Multi-Factor Authentication (MFA) Everywhere You Can: You know those crazy things your bank makes you do, credit card companies, retail sites, etc. It should also be used in your email applications, cloud applications, Admin accounts, finance systems. If it supports MFA, use it.
- Education: Constantly send out reminders related to strong passwords. Employees will hate you for these reminders so make them fun.
- Monitor, Monitor, Monitor: Monitor your systems for unusual activity. Advise your employees that if they are using the same password on retail sites and they know it was compromised to call IT or Information Security Team so they can review logs.
Final Thoughts:
Attackers are not guessing randomly. They are using automation, known passwords, and pattern analysis.
Passwords are not a suggestion, a personality test, or a creative writing assignment. It is just one gate that you can close.
We are here to help.
Contact us for any questions, concerns, and help with cybersecurity.
Email sales@pf-pulliam.comStay in the Loop & Get Help
Ready to make cybersecurity simple? Subscribe to the No Nonsense Series for exclusive tips. Or, if you need immediate help, reach out to our team!